Mythos is a new LLM (Large Language Model – AI) from AI company Anthropic. They’ve not released it publicly, but have been privately looking for vulnerabilities in browsers and operating systems. Anthropic claim it has found hundreds so far, and has formed Project Glasswing to work with major software vendors to resolve them. Heads of banks in the US and UK have been summoned at short notice to discuss the implications. Mythos has passed the UK’s AI Security Institute’s hardest, expert level, multi-stage hacking tests, and is the first LLM to get close.
Here at Lamplight we are starting to adapt to a world where software updates are needed daily or more. We are increasing our internal Information Security team and capabilities, and reviewing our existing practices. In our judgement, this will be a challenge for us all, personally and in our own organisations.
It’s Not Just Hype
Some commentary holds that this is sales hype. That’s wrong. The expert view from those already using LLMs to identify vulnerabilities is that “the capability is real, it is accelerating”. The UK AI Security Institute has tested Mythos. Mythos is the first model to fully solve “The Last Ones,” (TLO) AISI’s 32-step cyber range simulating an attack on a corporate network, “spanning initial reconnaissance through to full network takeover, which [AISI] estimate[s] to require humans 20 hours to complete.” Across ten attempts, Mythos averaged 22 completed steps and in three cases solved all 32. While there are some provisos to this, it’s still clearly highly capable. And it’s rapidly improving: on expert-level tasks — which no model could complete before April 2025 — Mythos Preview succeeds 73% of the time. The “cost of a full attempt is now around £65.”
Even if Anthropic are over-stating its capabilities, it’s clear that LLMs are already successfully being used to attack systems in lots of ways. The rate of progress is astonishing, and even if it’s not Mythos, it’ll be the next one or the one after that – in a few months time.
So What Does This Mean?
If “the good guys” are the only ones with this capability, there will be a lot of software updates coming our way. If the baddies access it, then lots of systems will be successfully attacked using previously unknown vulnerabilities, at a scale we’ve not seen before.
SANS are an authority on information security, and in a recent webinar they suggested that from a baseline of 40k vulnerabilities reported per year, we might see 2.4m vulnerabilities/year in the next 12 – 18 months. The hope is that that will drop again, eventually, as historical bugs are found and fixed, and our digital systems end up more robust and secure.
But in the meantime, if these sorts of numbers are correct, the rate of software updates will increase 600 times. Going from a monthly update to a daily update is a 30x rate increase. So 600x?
Isn’t this just the Fuss-About-Nothing Millenium Bug (Y2K) all over again?
For those of us old enough to remember, there were all sorts of dire warnings about financial systems collapsing and planes falling out of the sky on 1st January 2000. This was because the years in dates had been stored with two digits, and so come new years day, computers would think that the date was actually 1st January 1900.
In the event, nothing happened. The 1st January saw some nice fireworks and all the rest, but no calamity.
This isn’t because the IT industry had been crying wolf. The problem was real, and the warnings correct. What actually happened is that in the years leading up to the millennium, lots of people worked very hard to fix it. They succeeded, and we should be grateful.
“the risks were addressed by co-ordinated and timely action to mitigate them.” (National Preparedness Commission)
In my judgement, we are in a very similar position now. The threat is real, the updates are already increasing in tempo, and lots of people will be working hard to try and prevent some of the worst outcomes.
Risks and Implications
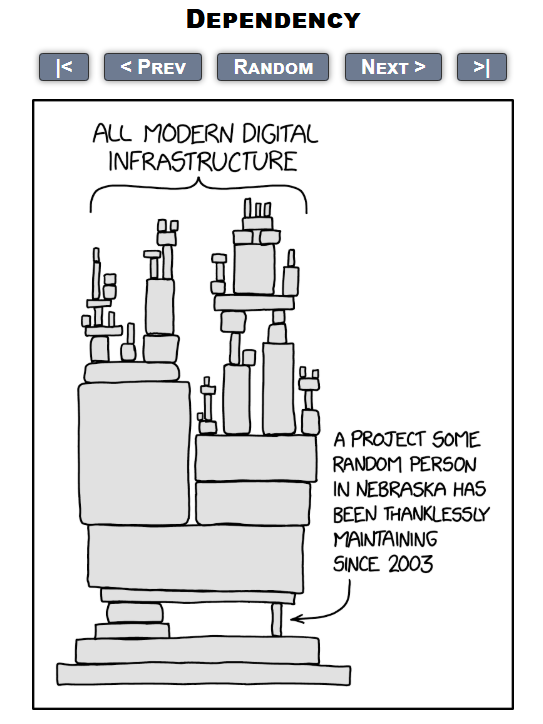
- Software depends on software depends on software. It’s like this jenga tower, but more so. And we’re going to be trying to take out all the pieces to fix them, all at the same time, and keep the tower standing. Some of the pieces are very old. Some don’t have the backing of big companies to resource updates. We’re already seeing open source software projects struggling to keep up with AI powered contributions. A lot of our digital world rely on open source software.
- Patching Velocity Will Increase. Hundreds of thousands of new previously unknown vulnerabilities covering all everything means that patching (updating) of all systems is likely to be more frequent and more urgent. We may need to accept (more) downtime for patching. Phones, laptops, servers, apps, social media, email, website, Amazon echo, cars, smart meters, TVs, Industrial control systems, home security system… everything will be updating all the time. We all need to find ways to manage that.
- Secondary Systems are not yet in scope: the partners for Project Glasswing include AWS, Microsoft, Linux Foundation among others. But there’s a lot more software in the world than that. Similar numbers of vulnerabilities exist in all of these systems too.
- Bad Actors Develop the Same Capability. They’ll already be trying, and possibly succeeding. Zero-day vulnerabilities are very valuable and there are significant financial incentives to find them. What was once the realm of highly skilled software engineers (whether good or bad) could become accessible to many more people. It will also be possible to look for vulnerabilities in minor targets which haven’t been worthwhile for humans. Even between the first and second draft of this blog it was reported that unauthorised people had accessed the Mythos model (although they weren’t “the baddies”).
- Dependency
Possible Responses
How to respond to this? We can share what we’re doing now – obviously your context will be different and this isn’t general advice.
- Reduce the number of suppliers of software to limit the scope of possible attacks. We are already planning to move from Zoom to Teams, and decommission Zoom. We should see how much further we can take this.
- Additional Information Security resourcing internally – adjusting team roles, more training to give us more capacity to manage what’s coming.
- Review and update our Patching Procedures to keep systems up to date.
- Explore how we can use LLM tools defensively to improve our security posture
- Prepare and Test Responses – can we handle more than one high-severity incident at a time? Or, how do we? What if the latest Windows update makes all our laptops unusable at the same time?
As you’ll know, we have ISO27001 in place which means that we have a good (and audited) Information Security Management System. This will give us the structure and management tools to oversee what we expect to be a challenging couple of years. We’re also in the process of applying for Cyber Essentials. If you’ve not done any of those sorts of things, Cyber Essentials is fairly accessible and will give you some assurance that the basics are in place.
Some useful links
Anthropic Previews Mythos Model
AISI’s Evaluation of Mythos’ Capability
Why Cyber Defenders Need to Be Ready for Frontier AI
Lessons from the Millenium Bug
Photo by KeepCoding on Unsplash






